Desi a trecut mai bine de un an de zile de cand Dev Team nu a mai scos o solutie de unlock pentru terminale iPhone, membrii sai impreuna cu membrii Chronic Dev Team vor vorbi la conferinta Hack In The Box despre Absinthe, Corona si evolutia baseband-urilor si a solutiilor de unlock pentru iPhone. MuscleNerd, Planetbeing, Pod2G, p0sixninja si pimskeks vor tine o prezentare la conferinta HITB ce va avea loc intre 21 – 25 mai in Amsterdam si vor discuta in detaliu despre dezvoltarea solutiei de untethered jailbreak pentru iOS 5 si despre cum au evoluat baseband-urile iPhone-urilor si cum nu au evoluat solutiile de unlock pentru iOS.
Cred ca prezentarea lor ar trebui sa fie interesanta si cred ca acolo vor prezenta motivele care i-au impiedicat sa mai lanseze solutii de unlock pana in prezent. Aceleasi motive ar putea fi valide si pentru absenta viitoarelor solutii de unlock.
Evolution of the iPhone Baseband and Unlocks
Joshua Hill (@p0sixninja), Cyril (@pod2g), Nikias Bassen (@pimskeks)Since the first iPhone in 2007, the baseband that Apple uses for cellular communications has evolved in terms of both hardware and software. Some of the changes were minor but others were quite drastic and obviously aimed at deterring carrier unlocks. This paper details the most interesting of the changes and what effects they’ve had on both software-based unlocks and hardware-based SIM interposers. In addition to comparing the most recent baseband against its own earlier hardware and software incarnations, we compare it to other current Qualcomm handsets and discuss the ramifications of changes Apple has made to the traditional Qualcomm baseband boot sequence. This presentation will cover:
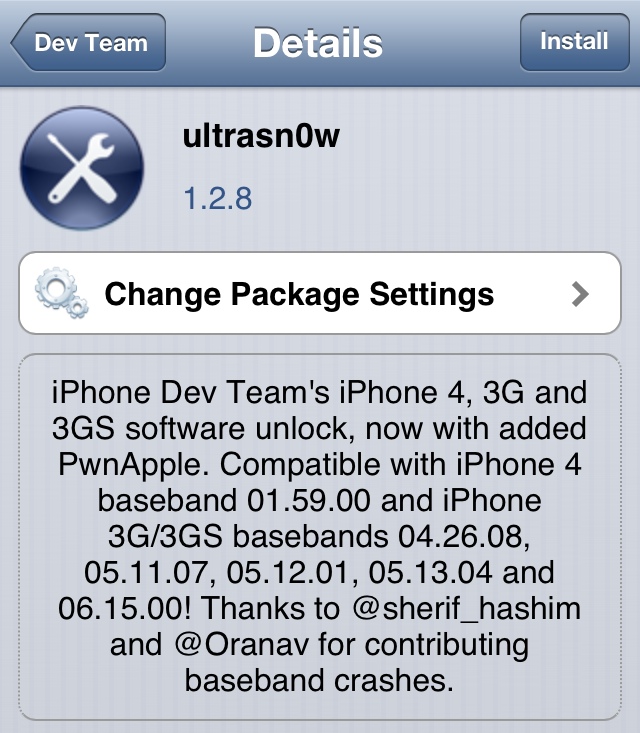
Baseband ROP: Overview of the role ROP plays in software unlocks like yellowsn0w and ultrasn0w. Comparison to ROP on the main Application-side CPU (jailbreaks). Why ROP wasn’t even necessary on the first generation of iPhones.
Software Unlocks vs. Hardware Unlocks: How iPhone software unlocks differ from those using hardware SIM interposers. Which layers of the baseband are exposed to each, and how the exploit development environment differs. Description of even more radical hacks like baseband chipset retrofitting and what Apple has done to prevent them.
iPhone4 DEP: How Apple implemented DEP with specific hardware changes on the iPhone4 baseband, and what went wrong. How ultrasn0w was made to work despite aggressive hardware-based DEP.
Operating Systems: So far, Apple has used 3 completely different baseband operating systems in the iPhone line. Description of which parts Apple tends to customize and why. Comparison of past and present custom command parsing.
Infineon vs. Qualcomm: Discussion of the transition from Infineon baseband chipsets to Qualcomm chipsets. Comparison of the older serial-based AT interface (still used on many other handsets) to the USB-based QMI used by the iPhone4S.
Activation Tickets: Detailed description of the “activation ticket” Apple uses to authorize use with specific (or all) carriers. How activation tickets interact with the traditional PIN-based NCK codes. Contrasting activation tickets and baseband tickets.
Baseband Tickets: Details on how Apple authenticates software updates to the baseband. Comparison of baseband tickets to “ApTickets” that Apple now uses on the main Application CPU to control software changes. Why baseband tickets provide even strong protection than ApTickets. The role of nonces in both the baseband and main application CPU.
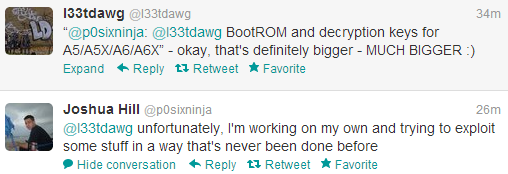
iPhone4S: What we’ve learned so far about the iPhone4S baseband. Overview of changes Apple has made to the original Qualcomm bootrom. How the iPhone4S baseband boot process differs from most other Qualcomm-based handsets. Which features the iPhone4S baseband has in common with other handsets and which have been removed. Description of the current attack surfaces, and comparing iPhone4 vs iPhone4S hardware-based protection mechanisms.